Your SOC,
In Your Pocket.
The first SIEM that detects threats and responds to them from your phone. AI-powered triage. Automated remediation. On-premise or cloud — you own it, running in minutes.
The first SIEM that detects threats and responds to them from your phone. AI-powered triage. Automated remediation. On-premise or cloud — you own it, running in minutes.
Install the SIEMLess server on any machine — bare metal, VM, or container. It’s a single binary. Working in minutes.
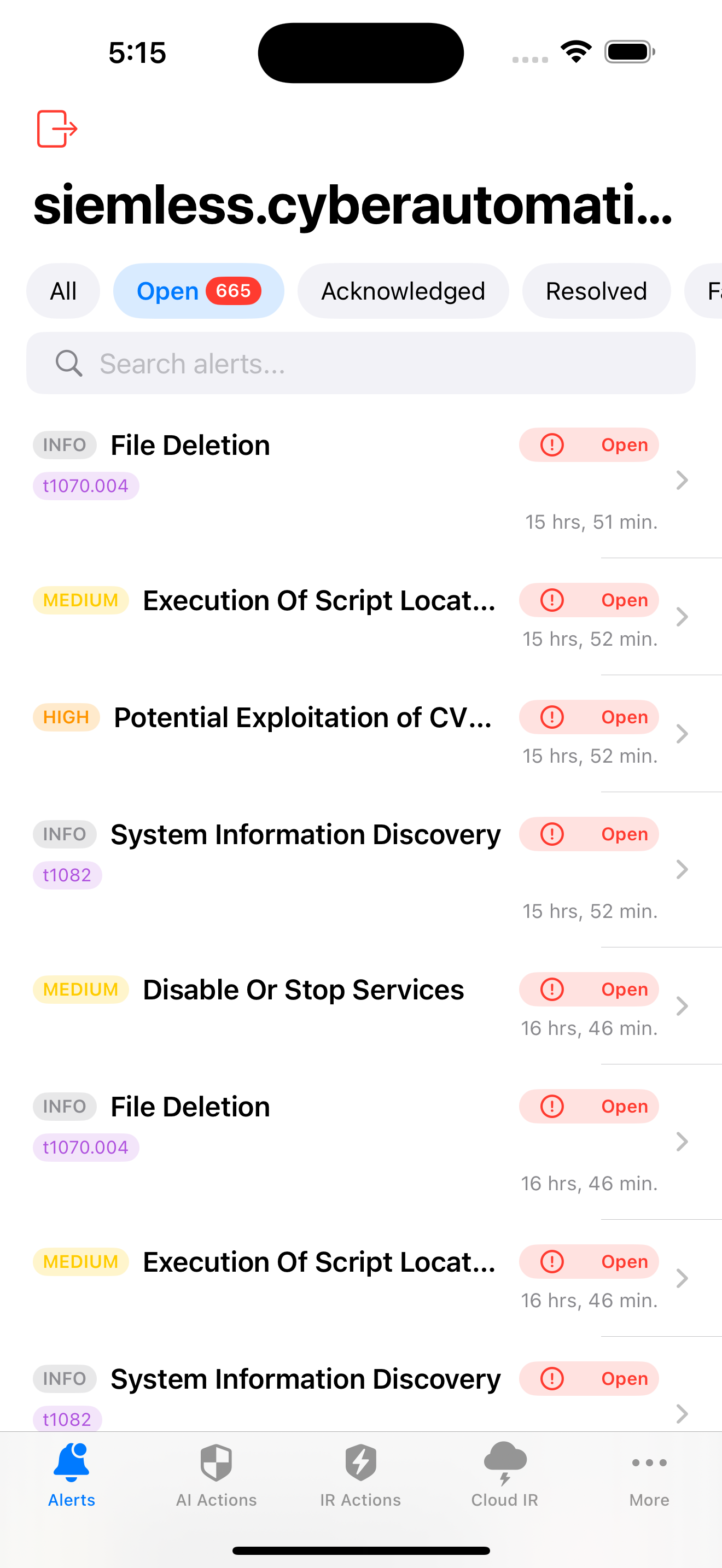
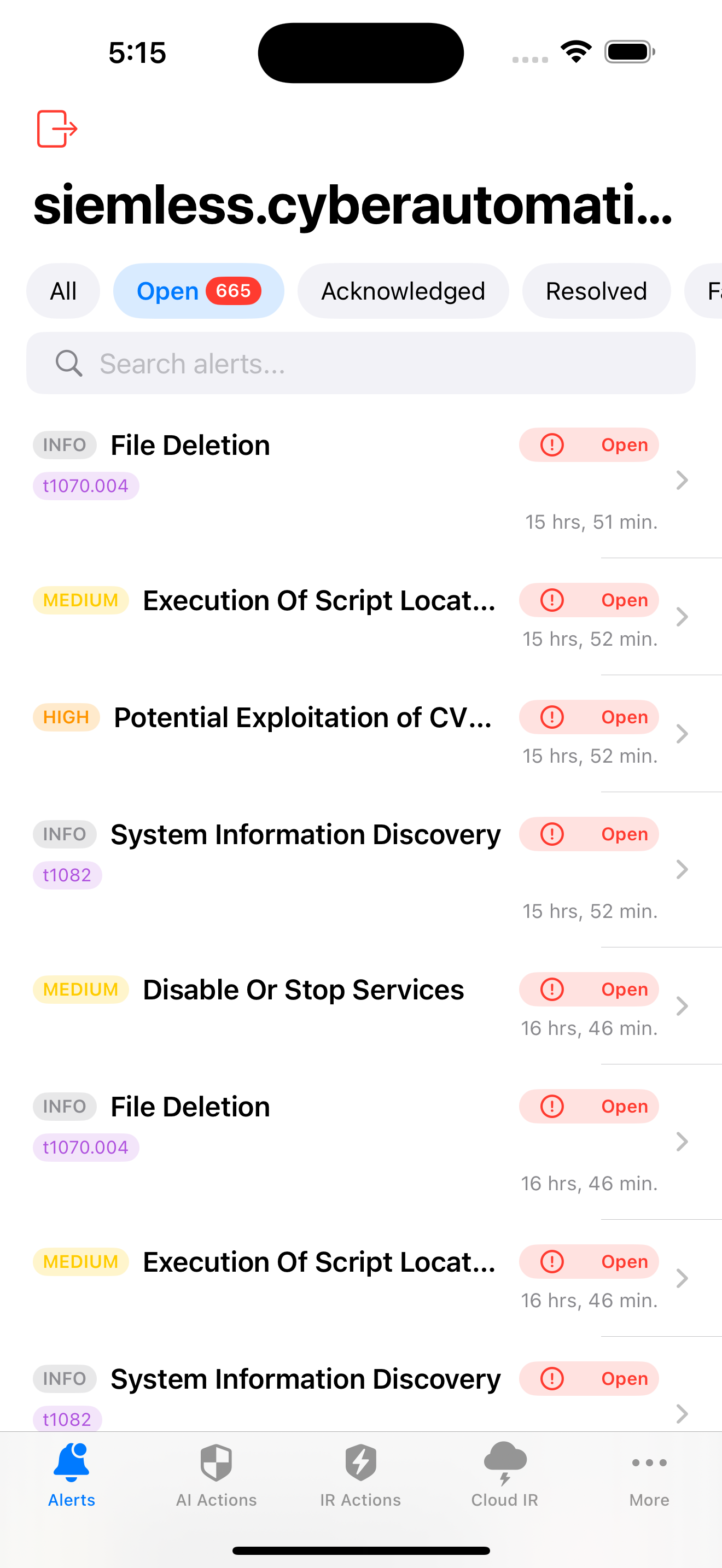
3,117+ Sigma rules with MITRE ATT&CK mapping start correlating events the moment agents connect. Syslog, cloud APIs, and file ingestion supported.
AI triages every alert. Automated actions — firewall blocks, user disabling, host isolation — execute from your phone or desktop with one tap.
CyberScore integration. 1-click ISM-compliant endpoint hardening, LOLBin blocking, and third-party patching — all triggered from the SIEMLess console.
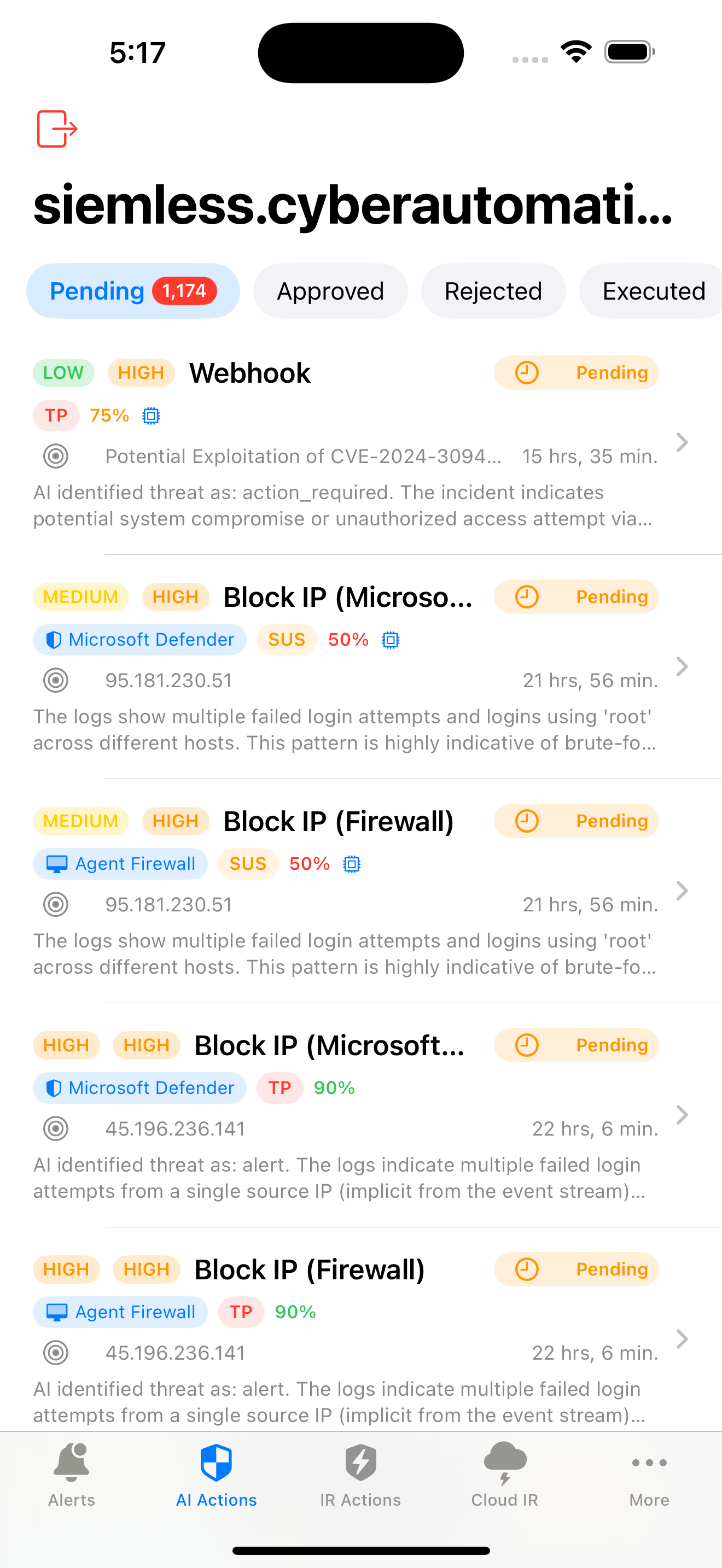
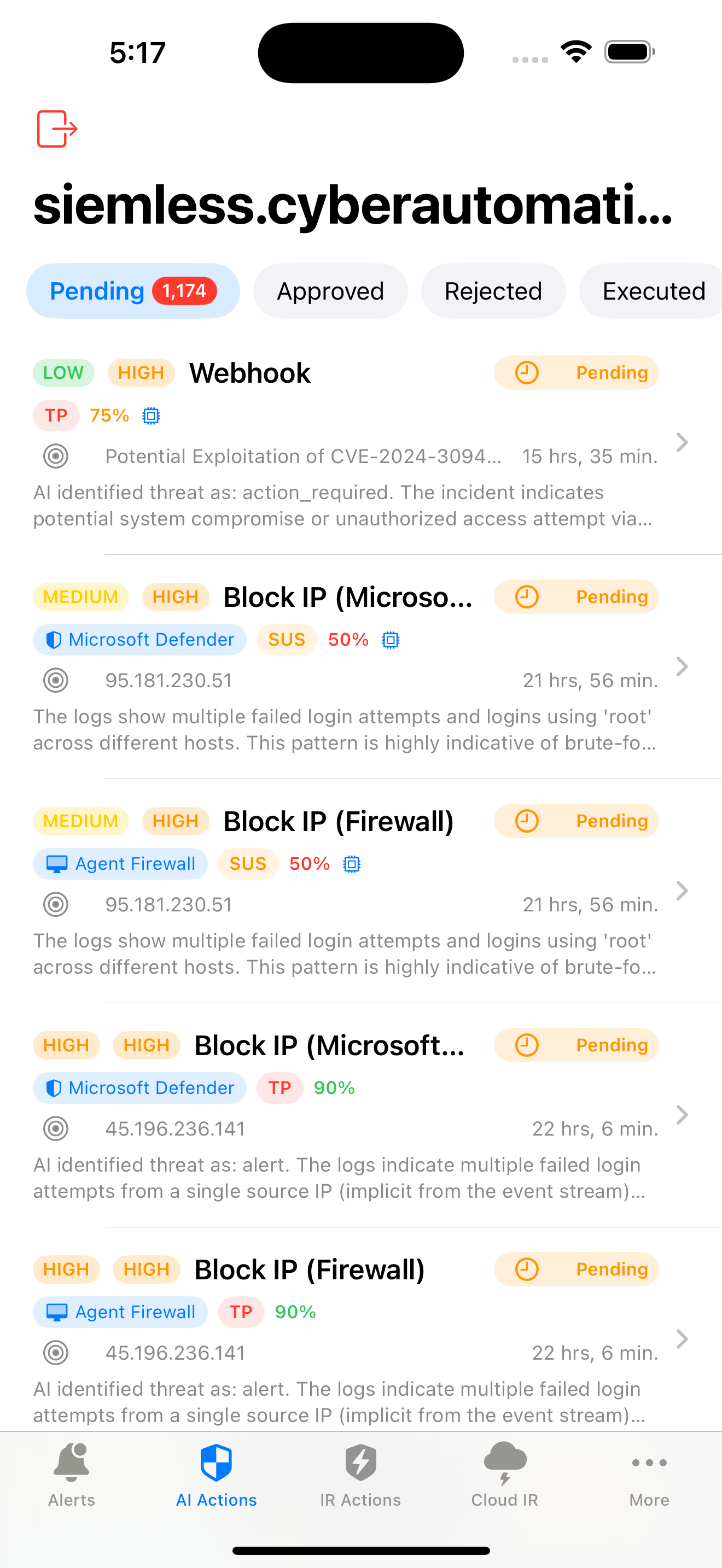
True positive, false positive, suspicious, or benign — with confidence scoring from 0–100%
AI generates response actions (block IP, isolate host, revoke sessions) ready for one-tap execution
Vector embeddings provide similar incident context for better classification accuracy
Run Ollama on-premise for fully disconnected environments. Your data never leaves your network.
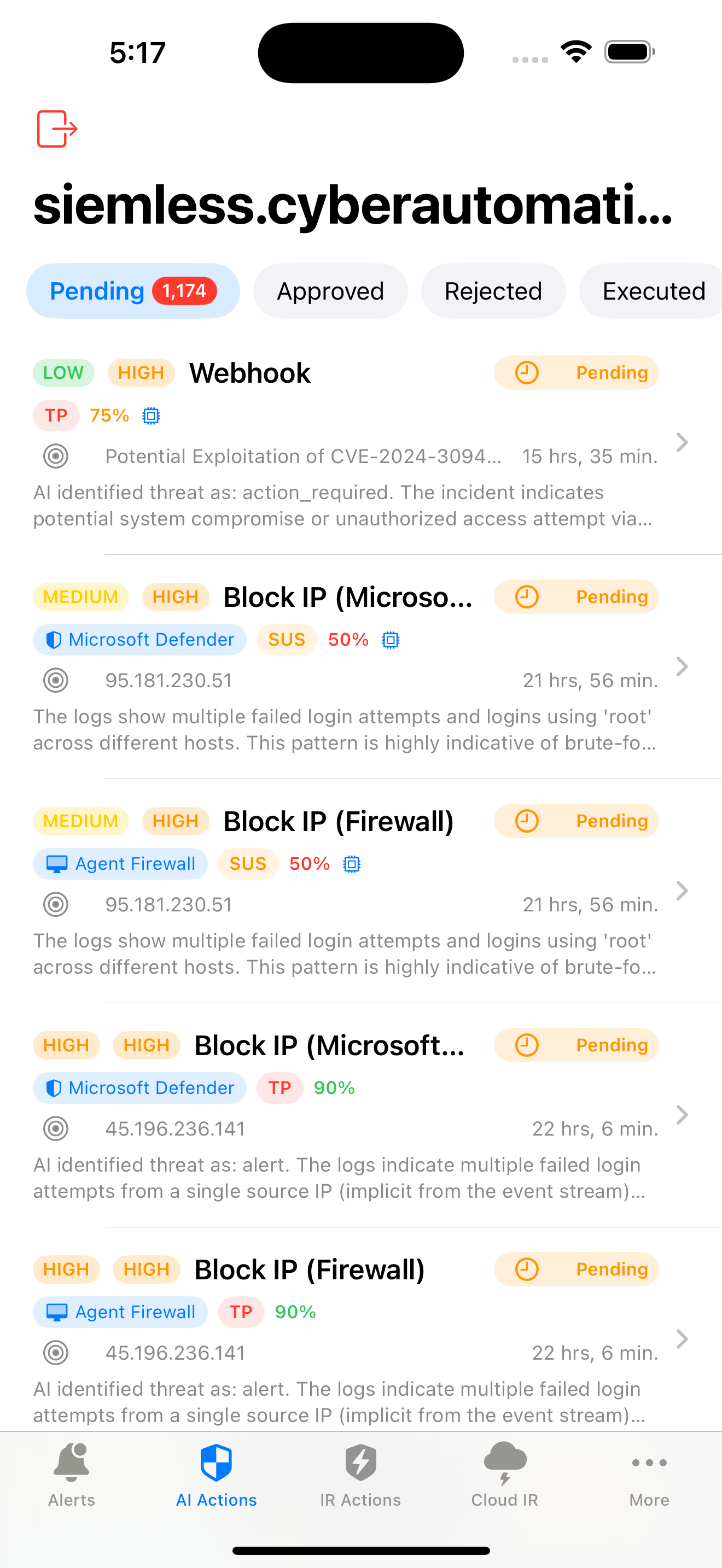
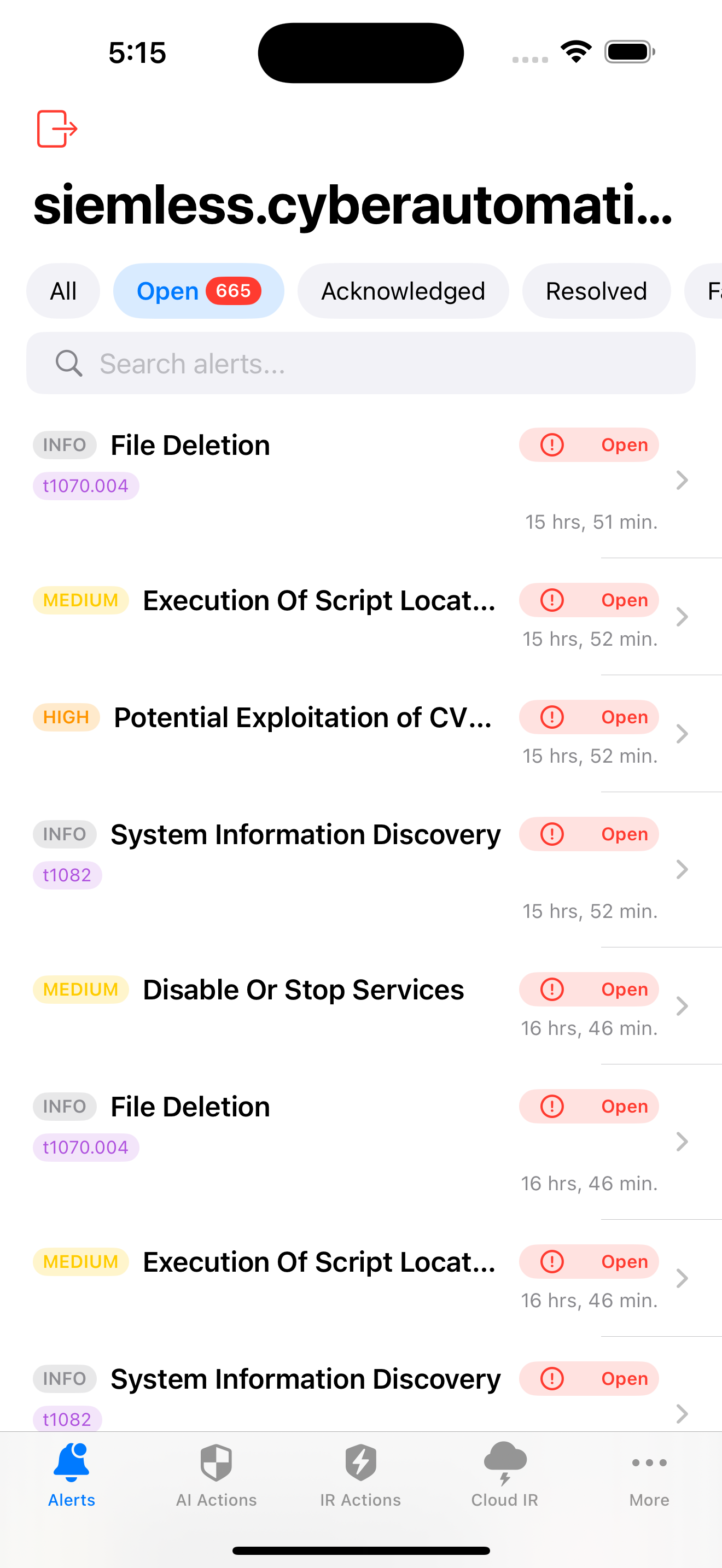
Real-time alerts with MITRE ATT&CK IDs and severity levels
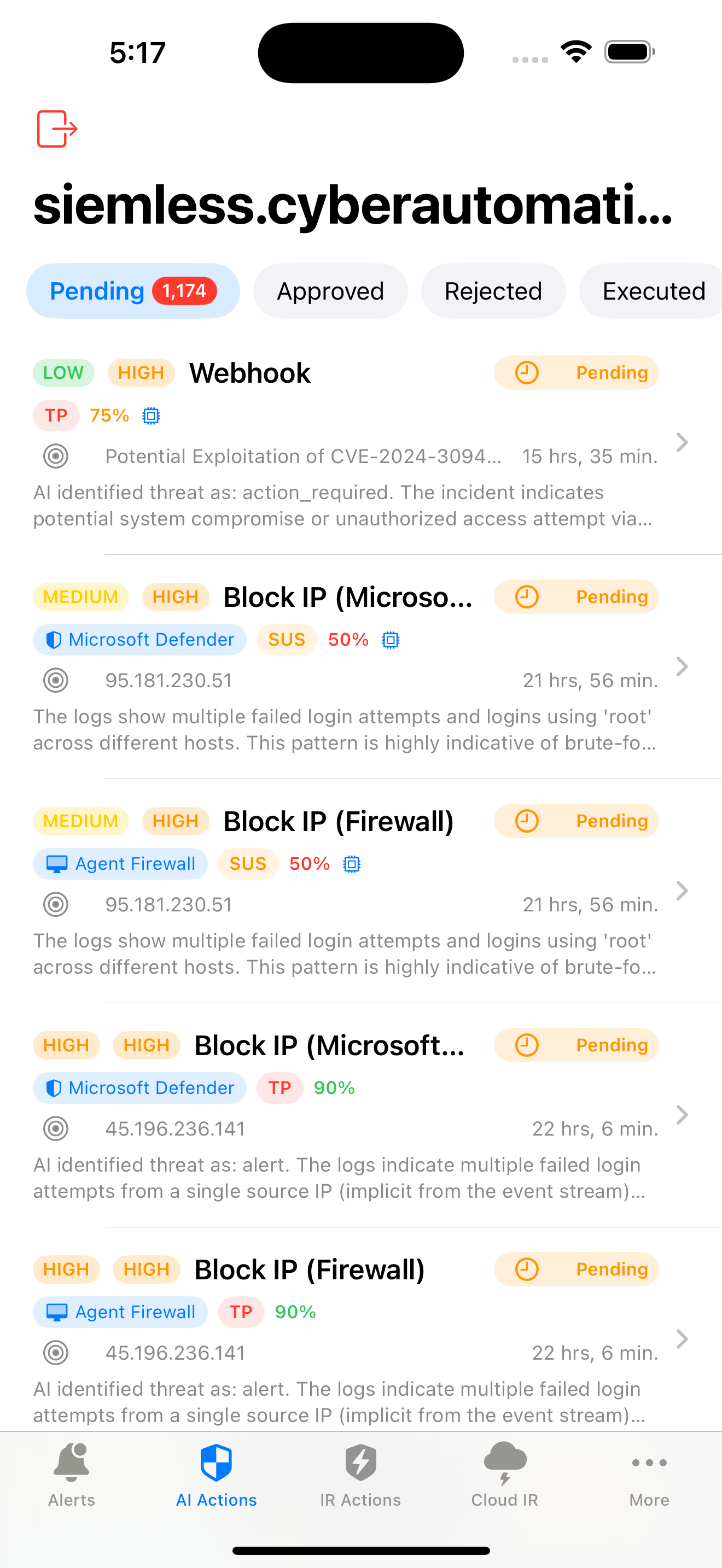
AI-generated verdicts and automated remediation actions
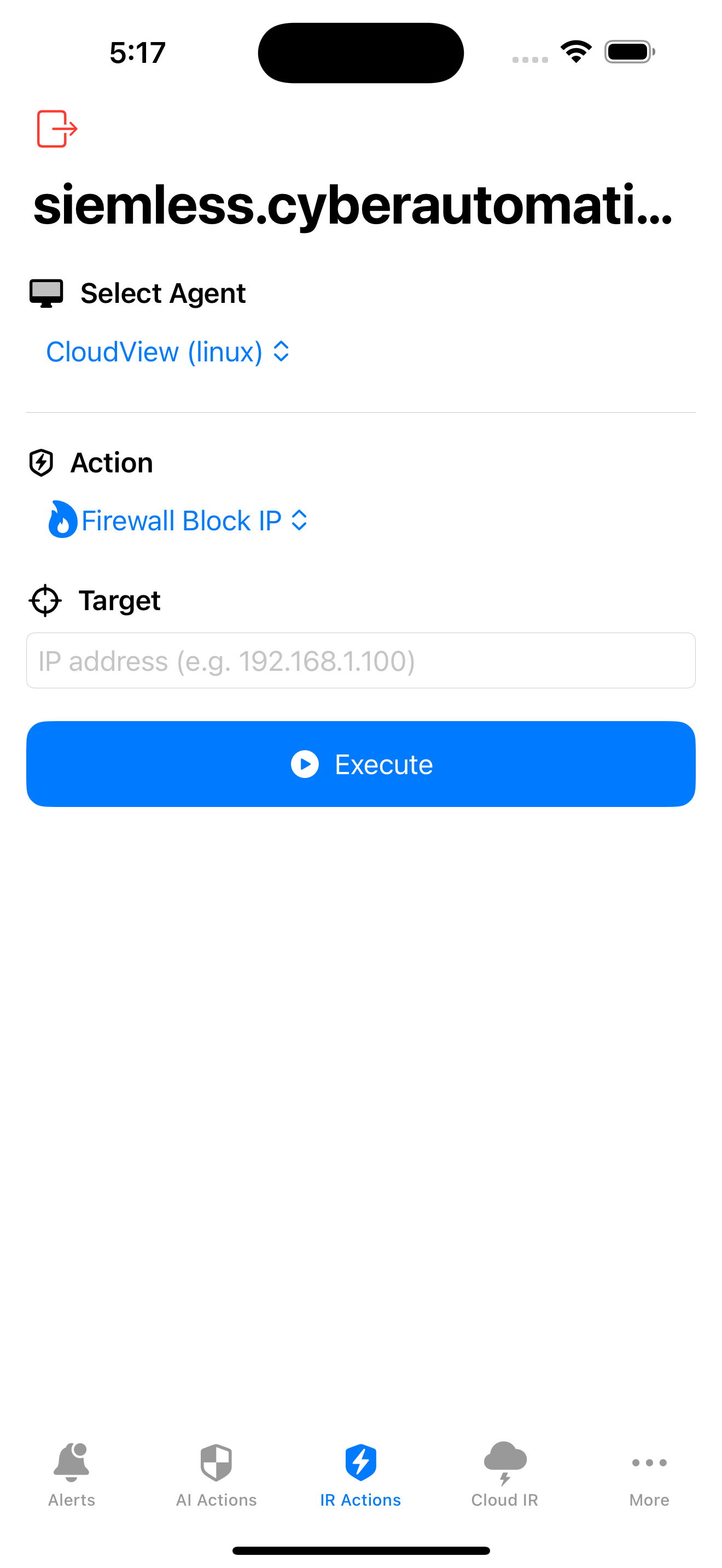
Block IPs, isolate hosts, disable users from your phone
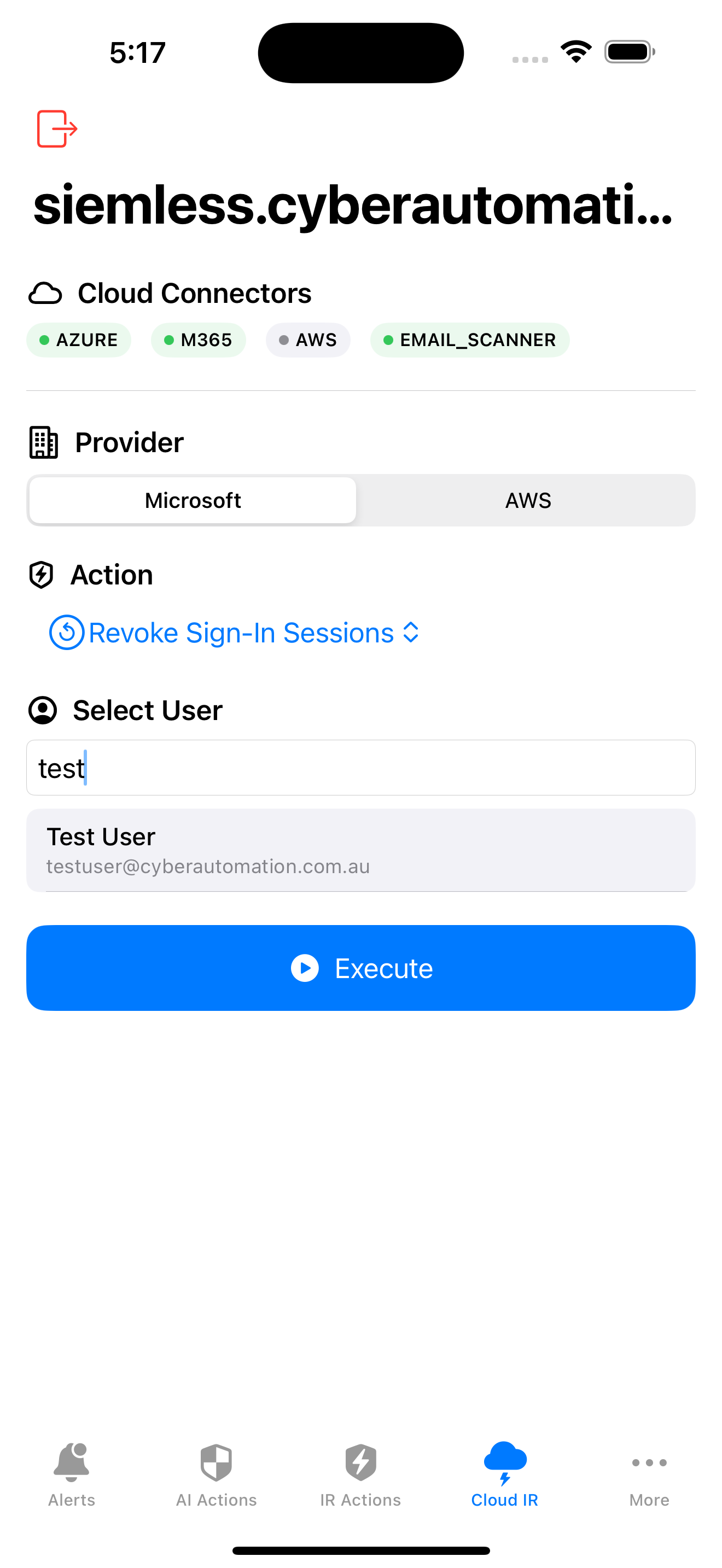
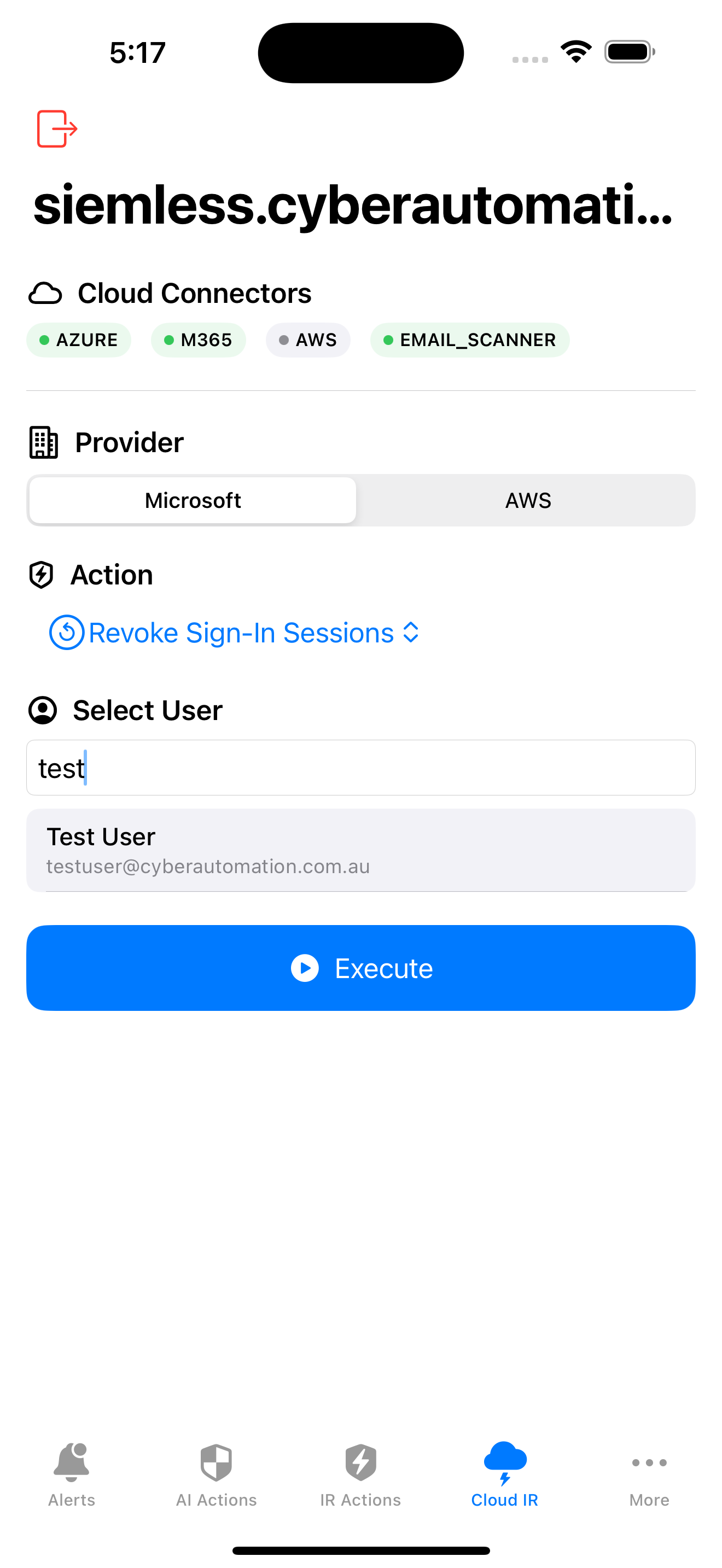
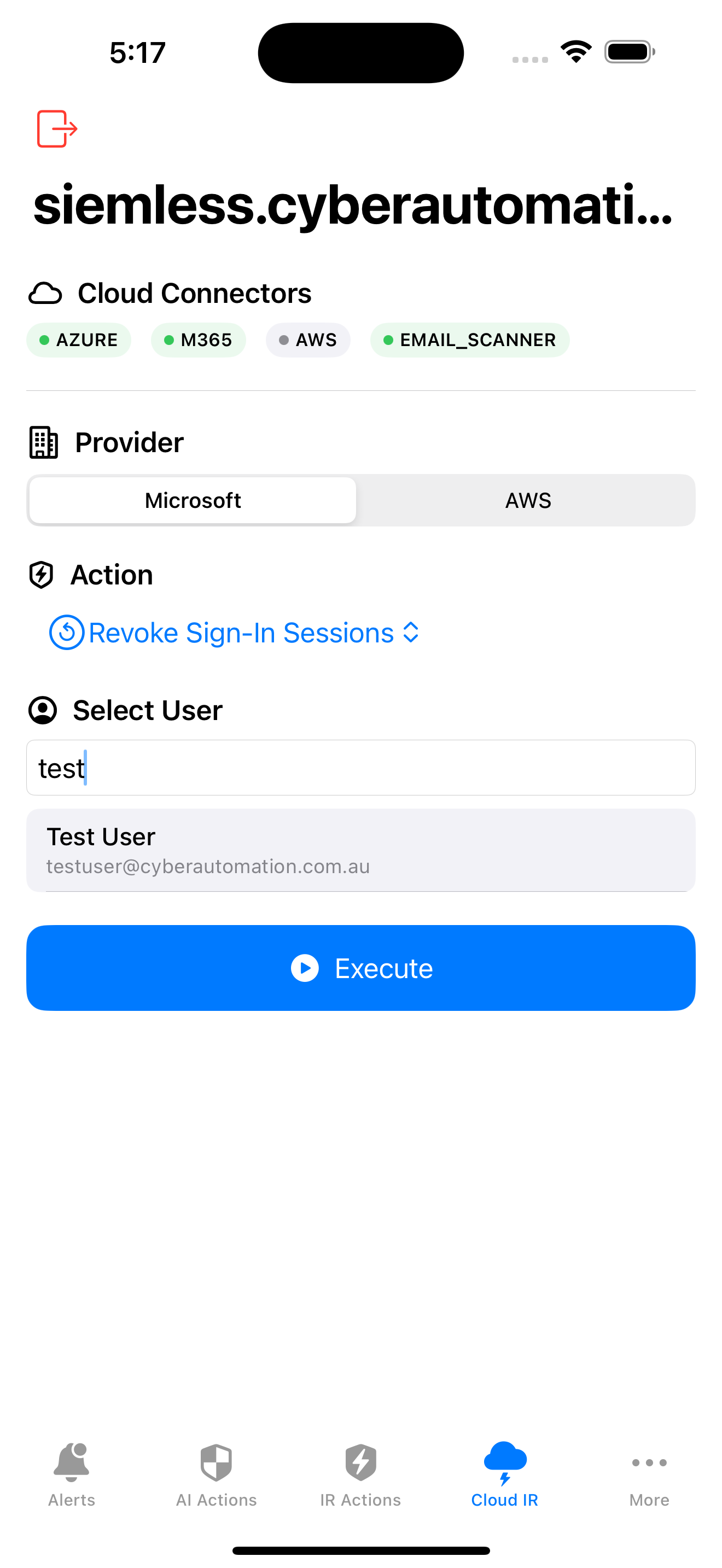
Revoke sessions, block access across Microsoft & AWS
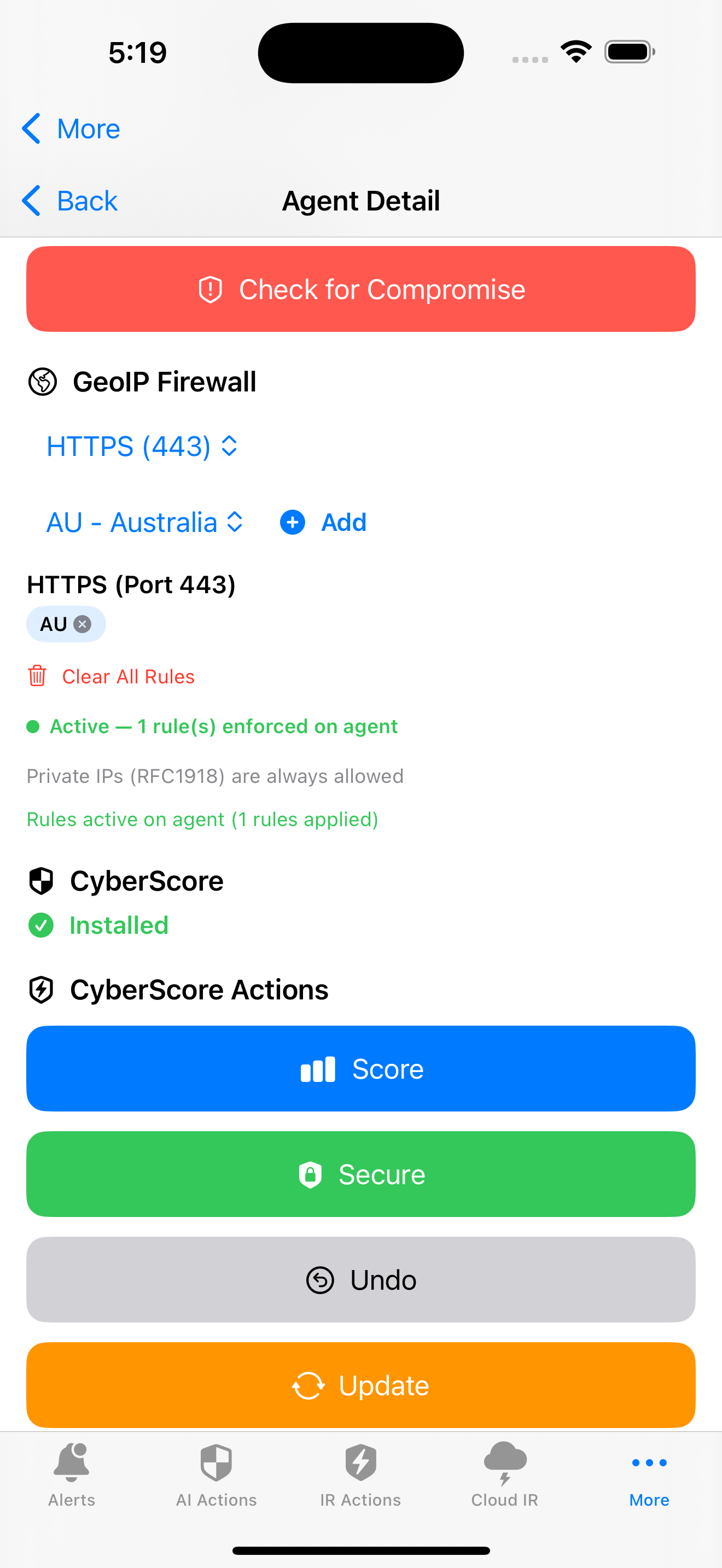
GeoIP firewall, CyberScore hardening, compromise checks
Process creation, registry changes, file events, network connections, authentication, DNS, script execution, cloud activity, web traffic, identity events, and more. Hot-reloadable without restart.
Every detection rule is tagged with MITRE ATT&CK techniques and tactics. Alerts surface with technique IDs so your team immediately understands the adversary’s playbook.
Endpoint agents, Syslog (UDP/TCP/TLS), file tailing, Azure Activity & Sign-in Logs, Microsoft 365 Audit, AWS CloudTrail, and proactive email scanning with phishing detection.
Proactive mailbox scanning across all users. URL reputation, attachment analysis, SPF/DKIM/DMARC validation, typosquat detection, and domain age verification via RDAP.
Identity-level incident response for compromised accounts.
Network indicators and email quarantine without touching the endpoint.
Cloud infrastructure response across IAM, WAF, and VPC layers.
ETW, Event Log, Registry, PowerShell capture
Audit pipe, XProtect, File events, DNS
Auditd, ProcMon, ClamAV, iptables
Kubernetes, Docker & pod telemetry
Mobile endpoint telemetry
Management console & push alerts
On-premise or cloud. You host it. You own it. Your data never leaves your network.